What is Port 4444?
by Erik Mikac | Published on February 18, 2025
Port 4444 can have several different purposes for multiple applications. Unlike your well-known ports like 80 and 443, this one is a little more cryptic. So, let's cover what port 4444 is and some of its applications.
Before delving into the many uses of port 4444, let's discuss what a computer port actually is. A computer port is a logical endpoint for communication. Software applications use it to send and receive data. Any application that needs network access will communicate via a port. For example, HTTPS requests typically use Port 443 for secure internet communication.
Port 4444 is one of many network ports available on your computer. In total, there are 65,536 network ports (ranging from 0 to 65535). Most ports are not reserved for a specific purpose. This allows different applications to use them as needed.
Now, let’s explore which applications are commonly associated with Port 4444.
Common Applications Using Port 4444
Port 4444 has several uses in the IT world. The most common usage is Oracle WebLogic Server. This port is often used as the default port for the myriad services associated with WebLogic.
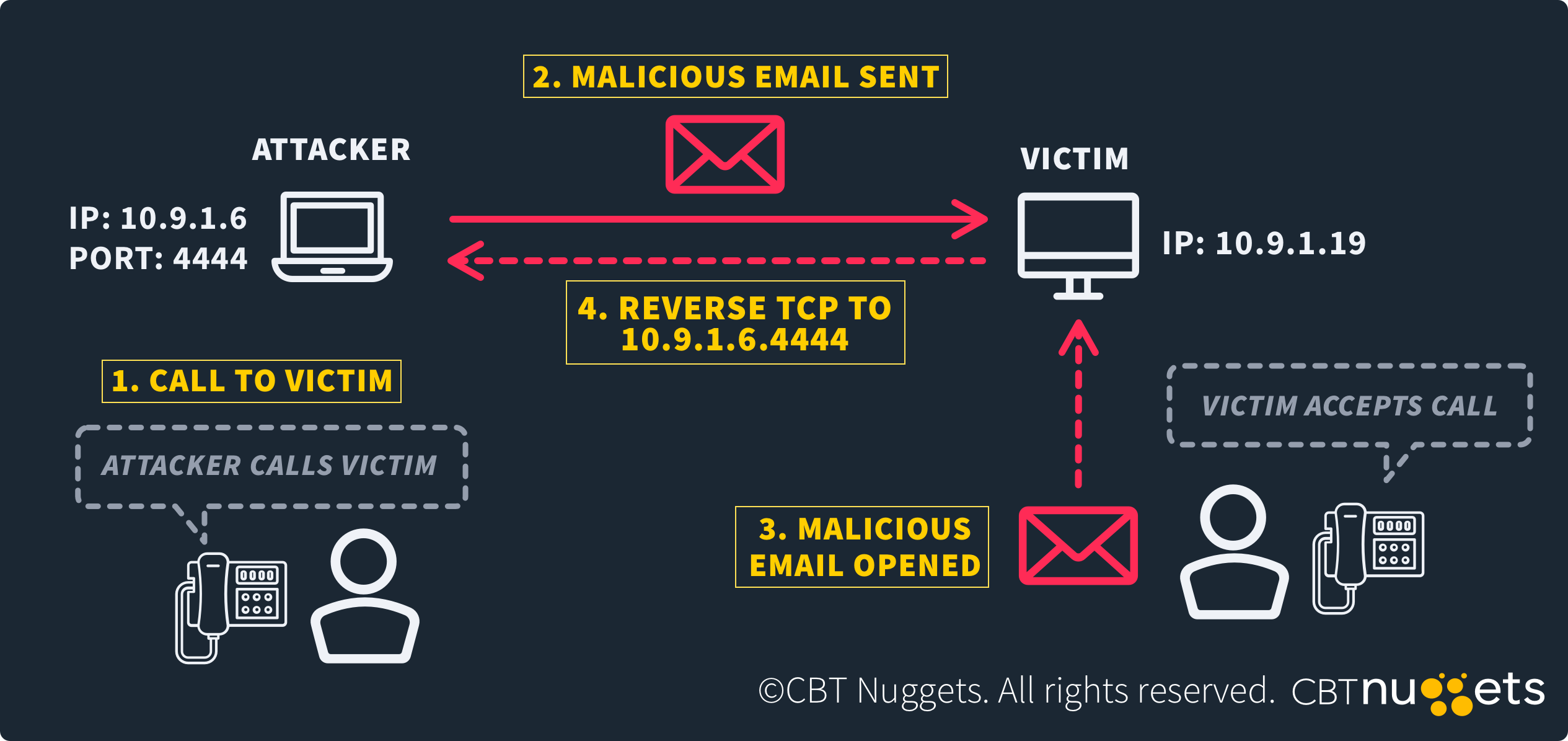
Metasploit also takes advantage of Port 4444. It uses Port 4444 as a reverse shell connector. A reverse shell is a type of connection where a compromised machine calls back to the attacker's machine. Once it's received, it gives them remote access. So, that means port 4444 listens to incoming connections from the exploited machine.
Python developers may recognize Port 4444 as the Jupyter Notebook port. Jupyter is a web-based interface used for writing, executing, and documenting Python code. Data scientists and AI engineers often use it to write machine learning code.
SAP Application servers often use port 4444 as well. An SAP Application Server is middleware that facilitates transactions between components of an SAP system. Some of these layers include the user interface, application logic, and databases.
Take into consideration that SAP systems are high-value targets for cyberattacks. So, keeping unnecessary ports like 4444 closed unless required is critical. In the event Port 4444 is open, check configurations and verify that it's used for its intended purpose.
Security Concerns and Measures
Port 4444 is not a designated port, so it is susceptible to exploitation. If it is open, a hacker could use it for unauthorized communication. As a general rule, close all unused ports. This is an essential part of zero-trust architecture.
If Port 4444 needs to be accessible, encrypt all data going through it. Use strong authentication mechanisms like MFA to ensure proper access. Another viable alternative is certificate-based authentication.
Metasploit uses Port 4444, so it's absolutely necessary that your firewall blocks it. Let's go over how to configure Port 4444.
Configuring Port 4444
When configuring Port 4444 (or any port) it's important to check if it's open. On Linux, that looks like this:
sudo netstat -tuln | grep 4444If that command returns nothing, then the port is closed. Another way to verify is by running this command from another machine:
nmap -p 4444 <target-ip>This will confirm that the port is indeed closed.
If the port is open and you need to close it, run this command:
sudo iptables -A INPUT -p tcp --dport 4444 -j REJECTThis ensures that no communication can leave or enter the port. On the other hand, if you want to open the port, run this command:
sudo iptables -A INPUT -p tcp --dport 4444 -j ACCEPTThose with a keen eye will notice it's the exact same as the last command, except now it says "ACCEPT." Remember to always keep Port 4444 closed unless it has a specific use.
Frequently Asked Questions
What is port 4444 used for in networking? Port 4444 is used by tools like Metasploit for reverse shell connections. It has some other applications for remote administration and communication, like SAP App Servers.
How can I secure port 4444 on my server? You can secure Port 4444 by closing it if it’s unnecessary. Use firewalls to block unauthorized access and implement (MFA). Lastly, monitor the port for suspicious activity.
Why is port 4444 often associated with security threats? Metasploit is the main reason you'll see hackers try and exploit Port 4444. If it's open, they can use Metasploit penetration tools for a reverse shell attack.
Which tools can I use to monitor port 4444 activity? Tools like Wireshark, Nmap, netstat, ss, and Zabbix can help monitor Port 4444 activity. All of them are great options for detecting unauthorized connections.
Can I change the default settings for port 4444? Yup, you sure can. Change the default settings for Port 4444 by configuring the application using it. Another option is to modify firewall rules to restrict traffic.
Final Thoughts
Port 4444 is a versatile yet potentially dangerous port. You'll see it used a lot by applications like WebLogic, Metasploit, and Jupyter. However, it's often associated with security exploits, too. Particularly penetration testing tools like Metasploit. With that said, it’s critical to manage this port carefully.
If Port 4444 isn't required, close it or at least restrict access. If it needs to be open, use MFA and other security measures like encryption to minimize risk. Maintain strict security practices, and you can use port 4444 to its fullest extent.
Interested in a career in cybersecurity? Our cybersecurity training is a great place to start.